Statement of Confidentiality
Red Team Security SRL is the creator of the material contained in this document and regards it as exclusive and sensitive business information. The use of this information is restricted solely to its designated purpose — to report cybersecurity analysis results to the client organization.
Releasing this document to any other vendor, business associate, or contractor is prohibited without Red Team Security SRL's express written authorization. It is forbidden to share, replicate, or disseminate any part of this document without explicit permission.
The information provided in this document should not be considered legal advice.
Engagement Contacts
| Client Contacts | ||
|---|---|---|
| Contact | Role | |
| [REDACTED] | Chief Executive Officer | [redacted]@[client].local |
| [REDACTED] | Chief Technical Officer | [redacted]@[client].local |
| Red Team Security SRL | ||
| Assessor | Role | |
| Andrei Grigoras | Lead Security Consultant | [email protected] |
Executive Summary
[ENTERPRISE CLIENT] engaged Red Team Security SRL to conduct an in-depth internal network penetration test. The aim was to uncover security flaws, assess their potential impact, systematically record results, and suggest corrective actions.
Assessment Strategy
Red Team Security SRL adopted a black-box testing methodology. The assessment ran from April 22 to April 29, 2024, with no prior access to credentials or knowledge of the client's internal network infrastructure. This approach was designed to uncover vulnerabilities that would not be visible to an automated scanner and to simulate what a real attacker with internal network access could achieve.
Tests were designed to be non-intrusive and were conducted remotely from a dedicated assessment host. Each detected vulnerability was meticulously recorded and examined for exploitability and lateral movement potential. Where the client sanctioned further access escalation, full attack chain scenarios including lateral movement, credential coercion, and privilege escalation were pursued.
Scope
The scope of this assessment covered 3 internal network ranges and one Active Directory domain:
| Host / IP Range | Description |
|---|---|
| 172.16.15.0/24 | [CLIENT] internal network 1 |
| 10.20.48.0/24 | [CLIENT] internal network 2 |
| 192.168.19.0/24 | [CLIENT] internal network 3 |
| [CLIENT].LOCAL | Active Directory domain |
Findings Overview
During the assessment, Red Team Security SRL identified seven findings that pose material risk to the client's information systems, plus one informational finding. None of the findings involved missing OS or third-party patches — every issue stemmed from misconfigurations or insufficient hardening, primarily in the areas of weak authentication and weak authorization.
The assessment resulted in full compromise of the [CLIENT].LOCAL Active Directory domain. The path to domain compromise relied on chaining several medium-severity issues, which individually appeared manageable but together created a clear attack path from zero access to Domain Admin.
| ID | Severity | Description |
|---|---|---|
| EC1-0424 | Critical | LLMNR/NBT-NS Response Spoofing — allows credential capture for any domain user via network poisoning |
| EH1-0424 | High | Weak Kerberos Authentication (Kerberoasting) — service accounts configured with weak, crackable passwords |
| EH2-0424 | High | Local Administrator Password Re-Use — same admin password across all servers enables lateral movement |
| EH3-0424 | High | Weak Active Directory Passwords — multiple domain accounts with easily guessable passwords |
| EH4-0424 | High | Tomcat Manager Weak/Default Credentials — admin interface exposed with default credentials |
| EM1-0424 | Medium | Insecure File Shares — excessive permissions allow all authenticated users to read sensitive shares |
| EL1-0424 | Low | Directory Listing Enabled — web server exposes directory structure to unauthenticated users |
| EI1-0424 | Info | Enhance Security Monitoring Capabilities — no detection of assessment activities was observed |
Vulnerability ID Convention
Each finding ID follows this convention: EC1-0424
Scope: Internal/External/Web/IoT/Mobile
Severity: C=Critical, H=High, M=Medium, L=Low, I=Info
Finding index for that severity level
Discovery date: April 2024
Internal Network Attack Chain
During the assessment, Red Team Security SRL gained a foothold and achieved full administrative control over the [CLIENT].LOCAL Active Directory domain. The steps below trace the path from initial access to full domain compromise. Any findings not used as part of this path are documented as standalone issues in the Technical Findings section.
The intent of the attack chain is to show the client how findings interconnect and to help prioritize remediation. Patching even two flaws in this chain would have broken the path to compromise.
Detailed Walkthrough
LLMNR/NBT-NS Poisoning — NTLMv2 Hash Capture
The Responder tool was started on the assessment host. By poisoning Link-Local Multicast Name Resolution (LLMNR) and NBT-NS traffic, the tool spoofed name resolution responses for a domain workstation that made a broadcast query. This caused the workstation to send its NTLMv2 authentication hash to the assessment host.
Offline Password Cracking — Clear-Text Credentials
The captured NTLMv2 hash was cracked offline using Hashcat with the rockyou wordlist. The clear-text password was recovered, granting initial authenticated access to the [CLIENT].LOCAL domain as a standard user.
Active Directory Enumeration — BloodHound & SPNs
BloodHound.py was run to enumerate the domain and build a graph of attack paths. Multiple privileged users were found configured with Service Principal Names (SPNs), making them targets for Kerberoasting — a technique where any domain user can request Kerberos TGS tickets encrypted with the service account's password hash.
Kerberoasting — Service Account TGS Ticket Cracked
A targeted Kerberoasting attack was performed against the svc_sql service account, which had been identified as having local administrator rights over a high-value database server. The TGS ticket was cracked offline using Hashcat, revealing the clear-text password.
Remote Access — LSA Secrets Dumped from Database Server
Using the cracked svc_sql credentials, the assessment host authenticated to the database server via SMB and dumped LSA secrets from the Windows registry. This revealed an autologon credential for a privileged service account that had local administrator rights across all servers in the domain.
Lateral Movement — Privileged User Session Found
Using the srvadmin credential, the assessment host authenticated to a member server via RDP. BloodHound confirmed that a user actively logged into this server had DCSync privileges over the domain object — granting the ability to extract the NTLM hash for any domain user via the DcSync attack.
Pass-the-Ticket — Kerberos TGT Stolen
Rubeus was used to extract the Kerberos TGT for the privileged user's active session. The ticket was injected into the assessment host's session, allowing full impersonation of this user without needing the clear-text password.
DCSync — Full Domain Compromise
Using the imported ticket, a DCSync attack was performed via Mimikatz. This technique replicates the Domain Controller's password database, granting the NTLM hash of every user in the domain including the krbtgt account — enabling Golden Ticket persistence and permanent domain compromise.
Technical Findings
Link-Local Multicast Name Resolution (LLMNR) and NetBIOS Name Service (NBT-NS) are legacy name resolution protocols that broadcast to the local network segment when DNS fails. Any host on the network can respond to these broadcasts, making it trivial for an attacker to poison responses and capture NTLMv2 credential hashes from any machine that falls back to these protocols. These hashes can then be cracked offline to recover clear-text passwords.
Any attacker who gains internal network access — whether through a compromised device, a rogue insider, or a misconfigured guest VLAN — can immediately begin passively collecting domain user credentials. This requires no privileges and is extremely difficult to detect. The captured credentials provide the initial foothold needed to pursue further access escalation.
- ›Short term: Disable LLMNR and NBT-NS via Group Policy across all systems in the domain
- ›Short term: Deploy detection rules for Responder-style poisoning on the network monitoring stack
- ›Long term: Enforce SMB signing across the domain to prevent relay attacks using captured hashes
Service Principal Names (SPNs) were configured on multiple service accounts with weak passwords. Any authenticated domain user can request Kerberos TGS tickets for these accounts. The tickets are encrypted with the service account's NTLM password hash and can be exported and cracked offline without generating any authentication events in the domain.
- ›Reset all SPN-configured service account passwords to 25+ character random strings
- ›Migrate service accounts to Group Managed Service Accounts (gMSA) which rotate passwords automatically
- ›Remove SPNs from accounts that do not require them
A single local administrator password was used across all servers in the domain. Once one server was compromised and the password was extracted from LSA secrets, the same credential was valid for lateral movement to every other server. This dramatically amplified the impact of a single account compromise.
- ›Deploy Microsoft LAPS (Local Administrator Password Solution) to generate unique, rotating local admin passwords for every machine
- ›Immediately rotate all local administrator passwords across the environment
The Apache Tomcat Manager web interface was accessible on an internal server with default credentials in place (tomcat:tomcat). The Tomcat Manager allows authenticated users to deploy arbitrary WAR (Web Application Archive) files, which is equivalent to remote code execution on the host. An attacker with internal network access can log in, upload a malicious WAR file containing a web shell, and gain command execution under the Tomcat service account.
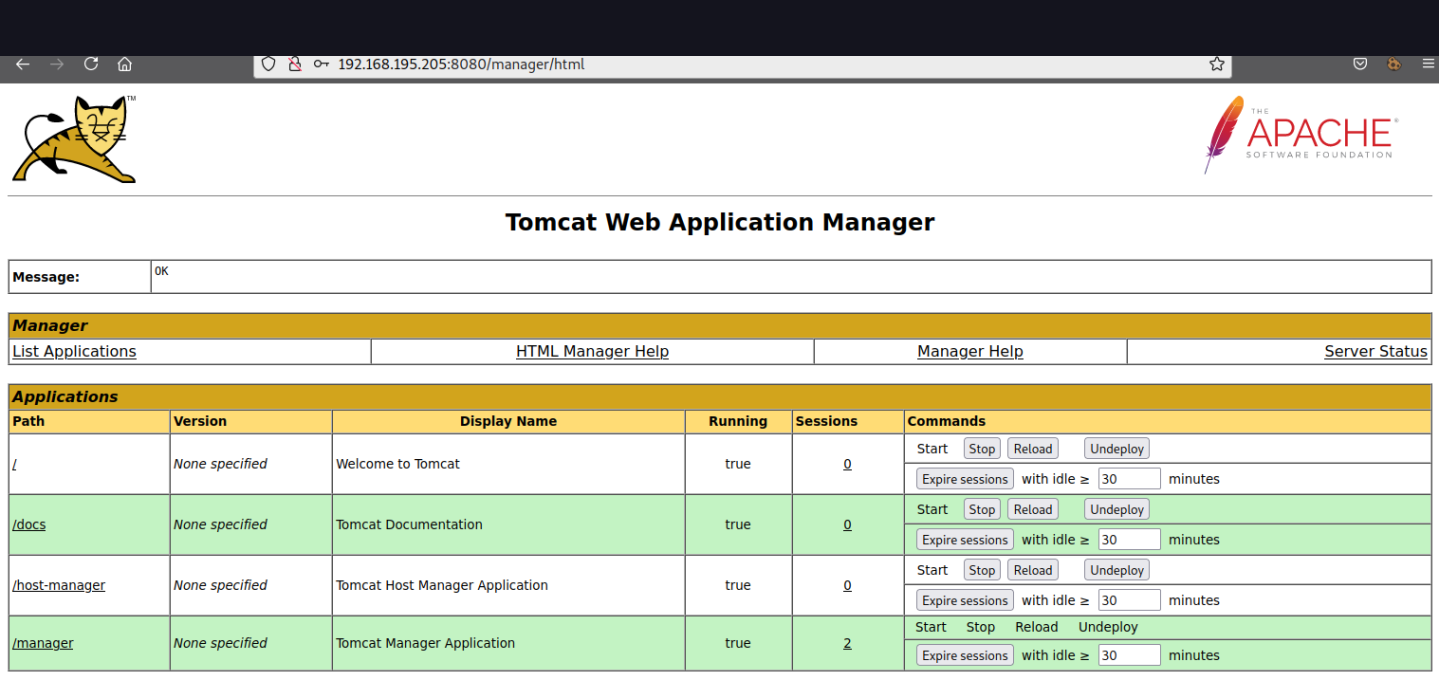
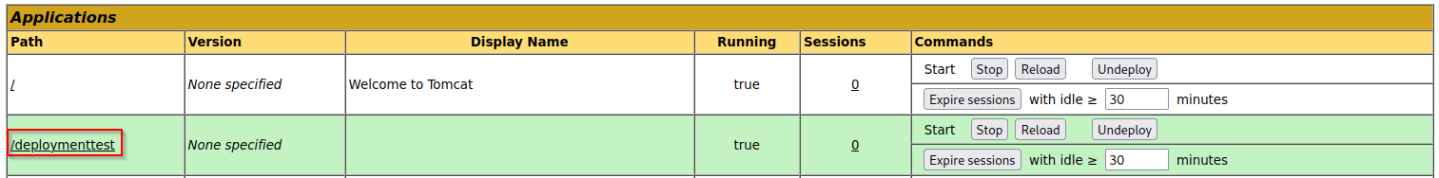
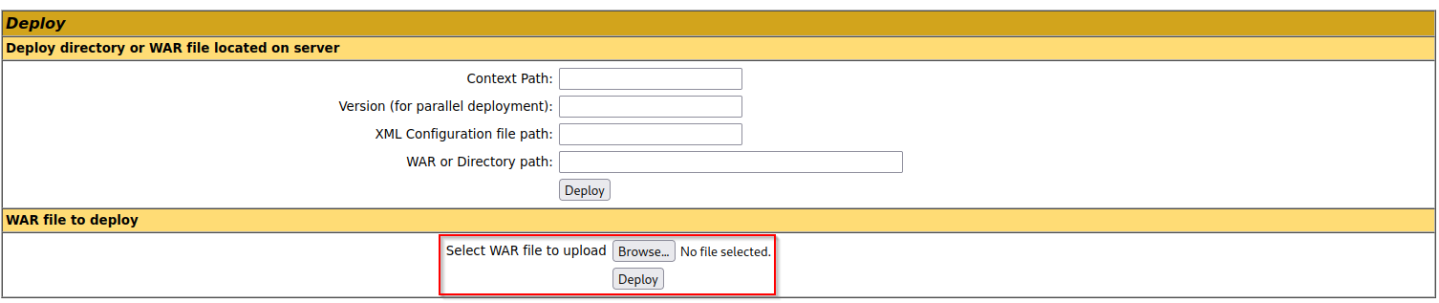
- ›Immediately: Change all default Tomcat Manager credentials to strong, unique passwords
- ›Short term: Restrict Manager interface access to trusted IP ranges via Tomcat's
context.xmlRemoteAddrValve - ›Long term: Disable the Manager application entirely if not required for production; use a dedicated deployment pipeline instead
Remediation Summary
| Timeline | ID | Action |
|---|---|---|
| Short Term | EC1-0424 | Disable LLMNR and NBT-NS via Group Policy domain-wide |
| Short Term | EH1-0424 | Reset all SPN service account passwords to 25+ character random values; evaluate gMSA migration |
| Short Term | EH2-0424 | Deploy Microsoft LAPS across all domain-joined systems and rotate all existing local admin passwords |
| Medium Term | EH3-0424 | Enforce a domain-wide password complexity and minimum length policy; run a password audit against the AD hash database |
| Medium Term | EH4-0424 | Change all default/weak credentials on the Tomcat Manager interface; restrict access to internal IPs only |
| Medium Term | EM1-0424 | Audit all SMB share permissions and apply least-privilege access control; remove authenticated-users permissions on sensitive shares |
| Long Term | EL1-0424 | Disable directory listing on all web servers; implement proper error page handling |
| Long Term | EI1-0424 | Implement a SIEM with detection rules for common Active Directory attack patterns (Responder, Kerberoasting, pass-the-hash, DCSync) |
Red Team Security SRL recommends addressing all Critical and High findings as a matter of urgency. Addressing the LLMNR/NBT-NS issue and deploying LAPS alone would have broken the attack chain demonstrated in this report. Once the above items are remediated, a follow-up Active Directory security review is recommended to identify any remaining attack paths.